In the last two blog posts I have presented two tools I use a lot. This week I want to continue with a third tool, that I have already briefly mentioned in my blog post Better security for WordPress with secure server headers: the Mozilla Observatory tool.
HTTP Observatory
When you run the tool for a domain, you first get an overview about the HTTP security. This was the part I’ve talked about in my previous blog post. The summary of the result may look like this:
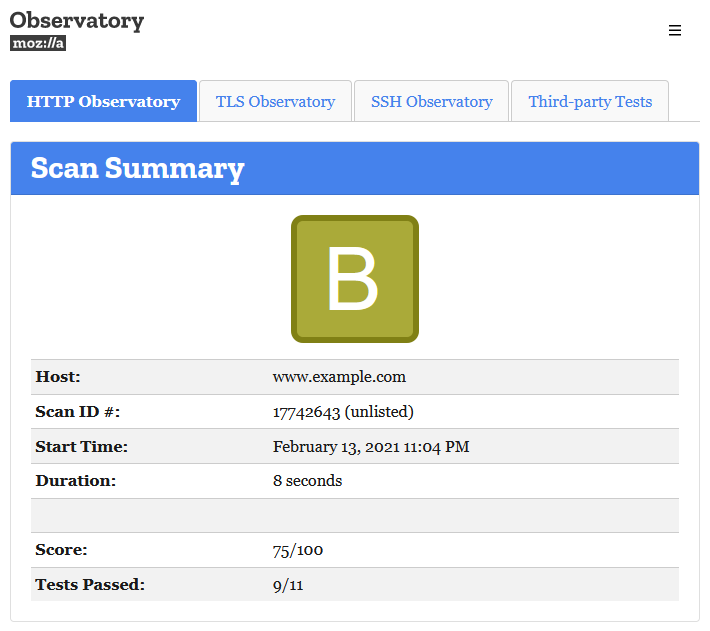
As the name of the tool indicated, the test is done using HTTP requests. At the end of the page you will find the Raw Server Headers for the request. Many of the values you will see here can also be found in the Test Scores and Content Security Policy Analysis sections. For each test result you will also find a link to the “Mozilla InfoSec” page.
TLS Observatory
The second tab will present you with details to the certificate. In the scan summary you may be recognize the “Compatibility Level” I have talked about in my previous posts. Here you can also check the validity of and the expiration time. The link behind the “Certificate Explainer” will give you even more “geeky” details about your certificate. At the bottom of the page you will find a button to the tool I wrote about in my blog post The perfect SSL configuration for your server.
SSH Observatory
In this tab you have to start the test manually. It will then give you some details about your general SSH configuration and if it passed the settings recommended by Mozilla.
Third-party Tests
In this last tab you may find some familiar tools. The first one is the ssllabs.com test result. The second one is from ImmuniWeb. This website will give you a lot of details about you website security. The third tool tls.imirhil.fr is focussing on the SSL ciphers. The securityheaders.com tool also offers many details, many of them can also be found in the other tabs. The last third-party tool hstspreload.org will check if the domain is included in the HSTS preload list.
Conclusion
The Mozilla Observatory is a great open source tool to scan the security status of your website. There is also a CLI tool you can use to make the same scans. You can also contribute to the website on the GitHub repository. If you configure your own server, I can highly recommend to give the tool a try to scan your domain.